*the digital version, that is.
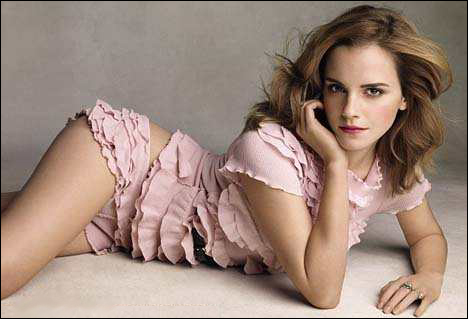
Emma Watson is World's Most Dangerous Celebrity
Harry Potter star Emma Watson is the favourite celebrity bait for cyber criminals trying to lure internet users, it has emerged. Internet security firm McAfee said today that the English actress is the 'most dangerous' celebrity to search for online.
That's because many sites use Miss Watson to trick users into downloading malicious software or to steal personal information. When searching for the 22-year-old, there's a one-in-eight chance of landing on a malicious site.
I'd add that the odds increase exponentially when the words "nude" or "topless" are included.
Dangerous!
Others on the top ten list include Jessica Biel, Eva Mendes, Selena Gomez, Halle Berry, Megan Fox, Salma Hayek, Sofia Vergara and Cameron Diaz, so kudos to the bandits for exhibiting exquisite taste. On the other hand, I've already initiated a law suit against them because Mila Kunis, my latest fave, was left off such a prestigious list.

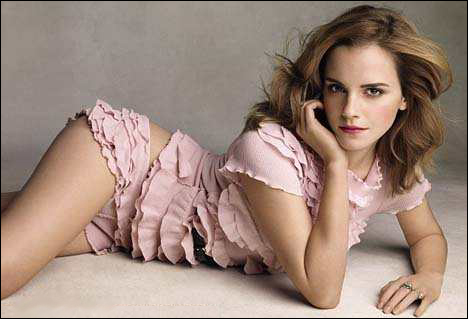
Extra dangerous!
And speaking of malware...
Bing Leads Google in Spam, Malware Search Results, Report Says
Nearly two-thirds of search results on Bing were found to have links that spread malware or spam, compared to 30 percent for Google, said Sophos Security in a recent study.
"Search engine poisoning," as it's called, affects all search engines; it might turn up the link you see first, or high up in results, for example, when you search for a popular celeb like Jessica Biel or Justin Bieber. Clicking on the link can take you to a spam site or, worse, one filled with malware aimed at infecting your computer.
And remember the cold, hard truth in all of this; that you don't deserve one tiny shred of sympathy should you get infected and not be able to immediately remedy the situation. And this cold, hard truth is because:
1. With free programs such as Windows Restore at the ready, which make a great big 'image file' of your entire system, you would normally just fire up the boot-up disc, load last week's image file and you're back in business within minutes.
and...
2. You shouldn't have been infected in the first place. A careful investigation after the fact will reveal that the free anti-malware program being used wasn't protecting the browser in real-time, allowing the infection to sneak through. This is known as you get what you pay for. It's a lesson that should have been learned long ago.
While Windows Restore does an adequate job, I prefer a commercial backup program called True Image. More info on both programs here. For an anti-malware program with real-time browser protection, I use ZoneAlarm.
As a small side note, image file backup programs aren't just for catastrophes. The other day I was curious if the Chrome browser had made any improvements since I last tried it a year ago, so I first made a backup file of the system, installed Chrome, played around with it for a while, was aghast that absolutely none of its major shortcomings had been addressed — then restored the original system via the backup file and it was as if the whole sordid event had never taken place. No muss, no fuss, no extra clutter of files on the system clogging things up.
This is known as owning a happy computer.